Patch prioritization for IT teams is essential in today’s security landscape, where threats evolve rapidly and demand a proactive stance. By tying patch management to business risk and real-world exposure, IT teams can focus on the most impactful security patches. Prioritizing updates that address critical vulnerabilities helps shrink the attacker’s window of opportunity through a clear, risk-based patching approach. A practical patch prioritization matrix guides decisions by balancing exploit likelihood, asset criticality, and operational impact. With robust testing, rollback plans, and governance, this framework keeps systems stable while accelerating remediation.
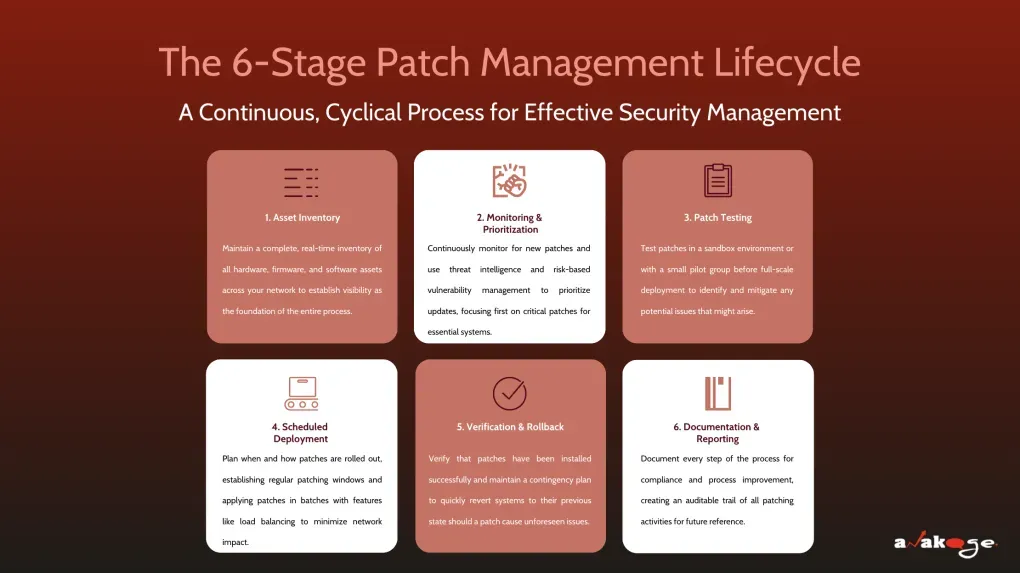
Viewed through an alternative lens, the concept becomes a risk-informed remediation sequence for security updates. From a vulnerability-management perspective, teams sequence fixes by exposure, asset value, and attacker interest, rather than by date alone. This approach emphasizes cadence, governance, and testing—a semantic family of ideas that aligns with LSI by linking related concepts like vulnerability, exposure, and remediation. Communicating in these terms helps security teams justify prioritization to executives and aligns patch work with regulatory expectations. Ultimately, a well-orchestrated patch lifecycle combines asset inventories, monitoring, and controls to reduce risk while preserving service levels.
Patch prioritization for IT teams: A risk-based framework for rapid remediation
Patch prioritization for IT teams is more effective when framed as a risk-based framework rather than a simple to-do list. By aligning patch management with the organization’s risk profile and business impact, teams can focus on security patches that close the most consequential gaps first, especially those tied to critical vulnerabilities. This approach helps balance security with uptime and operational continuity, ensuring that security controls scale with the enterprise.
A practical implementation relies on combining vulnerability data, threat intelligence, and asset criticality to drive decisions. Use CVSS context alongside exploit availability and exposure to refine risk scoring, and leverage a patch prioritization matrix to visualize and communicate priorities across stakeholders. The goal is a repeatable, transparent process that accelerates remediation without compromising system stability.
Leveraging a patch prioritization matrix to optimize patch management and reduce risk
A patch prioritization matrix translates complex risk signals into actionable deployment order. By mapping factor weightings—asset criticality, exposure, CVSS severity, exploit maturity, and business impact—teams can rank patches consistently across environments. This framework supports patch management programs by highlighting which security patches deliver the greatest risk reduction first, particularly for systems hosting sensitive data or delivering critical services.
Implementing the matrix requires discipline and governance. Regularly update asset inventories, classify systems by role, and maintain a centralized view of vulnerabilities and pending patches. When used in tandem with automated patch management tools, the matrix helps streamline testing, approval, and rollout, minimizing downtime while maximizing protection against security patches that address critical vulnerabilities.
Prioritizing critical vulnerabilities through risk-based patching and vulnerability management
Focusing on critical vulnerabilities is the essence of risk-based patching. Teams should triage advisories by combining vulnerability severity with exploit existence and real-world exploit activity. Prioritizing these patches reduces the window of exposure and protects assets most likely to be targeted by attackers, particularly internet-facing systems and databases holding sensitive information.
To operationalize this prioritization, integrate vulnerability management processes with change control and testing. Validate patches in a sandbox, plan staged deployments, and ensure robust rollback options. Communicate timelines and expected impacts to stakeholders, so remediation is predictable and aligns with both security objectives and business operations.
Integrating patch management with automated workflows and testing
Automation is essential for scaling patch management. Build automated workflows that detect missing updates, validate patches in a sandbox, and pilot them with a representative group before broad rollout. This approach protects critical services while accelerating remediation, and it supports continuous improvement of the patch management process.
A structured testing regime—covering compatibility, performance, and regression checks—reduces the risk that a patch introduces instability. Combine automation with change management to document approvals, deployment windows, and rollback steps. By segmenting environments (test, staging, production), IT teams can push security patches efficiently without disrupting business operations.
Expediting remediation: ensuring patch health and continuous improvement
After patches are deployed, monitor patch health to confirm that remediation is effective. Track indicators like mean time to remediation (MTTR) for high-risk vulnerabilities, post-patch system behavior, and any new issues introduced by updates. Security monitoring should verify that CVEs addressed by patches are mitigated and that detections are aligned with the updated environment.
Continuous improvement is essential to stay ahead of evolving threats. Regularly review patch scoring, adjust risk scores, and refine the patch management workflow. Use lessons learned from each cycle to fine-tune the patch prioritization matrix and improve the efficiency of patch management, ensuring that risk-based patching remains aligned with regulatory requirements and business priorities.
Measuring success with patch management metrics and business outcomes
A successful patch prioritization program demonstrates tangible outcomes, such as reduced MTTR for high-risk vulnerabilities, fewer unpatched critical vulnerabilities, and smoother audit trails for patch history. Align metrics with business goals to show how patch management reduces risk while maintaining service availability.
Leverage the patch prioritization matrix as a communication and governance tool. By linking patching activity to risk reduction and compliance objectives, organizations can justify resource allocation and demonstrate security improvements to leadership and regulators. This metrics-driven approach turns patch management from a compliance task into a strategic safety net for the enterprise.
Frequently Asked Questions
What is Patch prioritization for IT teams and how does it fit into patch management?
Patch prioritization for IT teams is the process of ranking patches by the risk they pose and the likelihood of exploitation. In practice, teams use data-driven criteria—such as CVSS scores, exploit availability, asset criticality, exposure, and potential business impact—and integrate this approach into patch management to ensure the most urgent fixes are applied promptly while preserving stability.
How does risk-based patching influence Patch prioritization for IT teams?
In Patch prioritization for IT teams, risk-based patching means assigning scores to patches based on likelihood of exploit and potential business impact. This helps prioritize security patches and other updates by focusing on high-risk vulnerabilities first within the broader patch management workflow.
What is a patch prioritization matrix and how should IT teams use it?
A patch prioritization matrix is a decision tool IT teams use to rank patches by risk and impact. By mapping factors like CVSS, exploit availability, asset criticality, and exposure, the matrix guides deployment order and balances speed with stability within patch management.
Why are critical vulnerabilities central to Patch prioritization for IT teams?
Critical vulnerabilities drive Patch prioritization for IT teams because fixing them reduces the window of exposure. Prioritizing security patches for these flaws helps reduce potential breaches while aligning with risk-based patching and compliance requirements.
Which factors should influence the order of patches in Patch prioritization for IT teams?
Key factors influencing the order of patches in Patch prioritization for IT teams include CVSS severity, exploit availability, asset criticality, exposure, regulatory requirements, testing results, and potential business impact.
What steps make up an effective Patch prioritization for IT teams workflow this quarter?
An effective Patch prioritization for IT teams workflow this quarter includes: building an asset inventory and classification; applying risk scoring and CVSS context; assessing exposure; testing patches in a sandbox; enforcing change management with rollback plans; scheduling deployment and communicating downtime; and monitoring post-patch health for continuous improvement.
| Key Point | Description |
|---|---|
| What patch prioritization for IT teams is | The process of ranking patches by the risk they pose to an organization and the likelihood that exploiting a vulnerability would cause real harm. It uses data-driven criteria such as CVSS scores, exploit availability, asset criticality, exposure, and potential business impact to decide which patches are addressed first. |
| Why prioritization matters | Prioritization reduces the window of exposure by tackling critical vulnerabilities first, aligns remediation with business risk and regulatory obligations, improves change-control efficiency, balances security with user experience and uptime, and builds a repeatable, scalable vulnerability remediation workflow. |
| A practical framework for prioritizing patches |
|
| Top patches your IT team should prioritize this quarter |
|
| Integrating patches into your workflow |
|
| Measuring success |
|