Software patches are small, targeted updates that fix known issues in software products. They address security vulnerabilities, critical bugs, performance glitches, and compatibility problems. When deployed correctly, patches deliver improvements without requiring users to replace entire applications. Thinking of patches as ongoing maintenance and part of patch management helps you keep tools reliable, secure, and up to date, while aligning with routine software updates. This introductory guide explains what patches are, why they matter, and how to install patches effectively, helping you protect systems, minimize downtime, and optimize performance.
In practical terms, these bite-sized fixes are delivered as patches, updates, or remediation releases that address flaws and strengthen defenses. From a search-friendly perspective, terms like security updates, bug fixes, maintenance releases, and compatibility improvements signal the same underlying activity. The goal is to plan, test, and roll out these changes gradually to reduce disruption and ensure compatibility with your environment. Consider leveraging a patch management mindset that coordinates inventory, testing, approvals, and staged deployment. By framing the topic with related ideas like vulnerability remediation, stability enhancements, and performance tweaks, you align technical work with broader IT objectives.
1) Understanding software patches and their role in modern IT hygiene
Software patches are targeted updates that fix flaws, improve performance, and close security gaps within software products. They are the practical mechanism by which developers deliver incremental changes—often without requiring a full rebuild of the application—and they sit alongside broader concepts like software updates and patch management as part of ongoing IT maintenance.
Recognizing the role of software patches helps organizations keep systems reliable, compliant, and up to date. By integrating these patches into a disciplined process, teams can reduce downtime, prevent data loss, and strengthen defenses against evolving threats while maintaining compatibility with other tools and environments.
2) Patch management as the cornerstone of secure, compliant environments
Patch management is the structured practice of discovering, evaluating, testing, deploying, and monitoring patches across a technology estate. It aligns with security patches, software updates, and governance requirements to reduce risk and ensure predictable behavior across devices and applications.
A robust patch management program emphasizes inventory, policy definition, and controlled rollout. By prioritizing patches based on severity and business impact, organizations can close critical vulnerabilities promptly and maintain compliance with regulatory and industry standards.
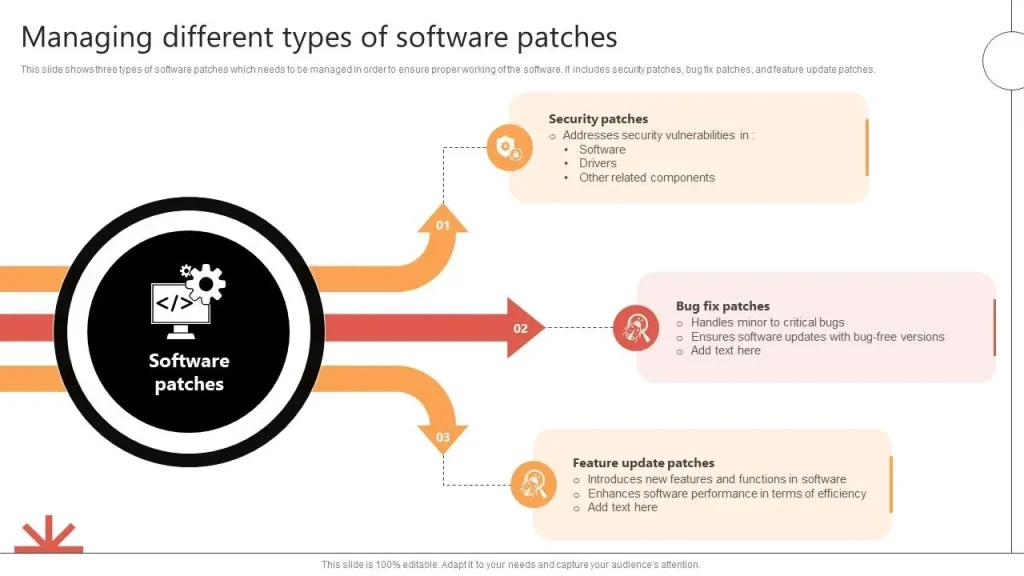
3) Prioritizing patch types to maximize security and reliability
Patches come in several forms, including security patches that close vulnerabilities, bug fixes that correct defects, feature patches that refine usability, and critical patches that address urgent issues. Understanding these types helps IT teams allocate time and resources where they matter most.
Effective prioritization in patch management weighs factors such as vulnerability severity, exploit familiarity, system criticality, and potential operational impact. This approach supports a balanced strategy that protects endpoints while avoiding unnecessary disruptions to production.
4) From discovery to deployment: the patch development lifecycle
Patches typically travel through a lifecycle: discovery, triage, development, testing, release, and deployment. Each stage aims to identify the issue, assess urgency, craft a fix, validate compatibility, and deliver updates to users.
Thorough testing and clear release notes help organizations understand what a patch changes and how it interacts with existing configurations. A well-planned deployment minimizes risk and makes it easier to track the effectiveness of each update once it’s applied.
5) Practical steps for installing patches across platforms
To install patches effectively, start with a data-backed baseline, review release notes, and plan for downtime if necessary. The process usually includes backing up critical data, validating patch applicability, and then applying the update while monitoring outcomes.
Platform-aware guidance matters: Windows environments may use WSUS or Microsoft Update, macOS relies on System Preferences or MDM, Linux distributions deploy via package managers like apt or yum, and mobile devices follow platform-specific update policies. Throughout, consider how to balance speed with safety by following best practices in patch management and documenting results.
6) Automating patch management for scalable security and efficiency
Automation scales patch management to large or dynamic environments, reducing manual errors and speeding up deployment. Central management tools, configuration management systems, and scheduled scans help enforce consistent patching policies and integrate vulnerability data into prioritization.
By tying patch management to vulnerability scanning and security workflows, organizations can close gaps more quickly and demonstrate compliance. Tools such as WSUS, SCCM, Ansible, Puppet, and Chef enable automated rollout, tracking, and rollback planning, ensuring that software updates—including security patches and other fixes—are applied reliably across all devices.
Frequently Asked Questions
What are software patches and why are they important for software updates and security patches?
Software patches are small, targeted code updates that fix bugs, close security vulnerabilities, and sometimes improve performance. They are a core part of patch management and are delivered as software updates by vendors, open‑source projects, or independent developers. Regularly applying patches helps reduce risk, improve stability, and keep systems compliant with security best practices.
How to install patches across different platforms as part of patch management, and what steps should you follow for reliability?
A platform‑aware approach works best. Back up important data, read the release notes, and test patches in a controlled environment before deployment. Use platform tools to install patches: Windows Update or WSUS for Windows, MDM or System Preferences for macOS, and package managers (apt, yum, dnf, zypper) for Linux. After installation, verify services are running and monitor performance to confirm success.
What is the patch management lifecycle, and how does it flow from discovery to deployment?
Patches typically go through a lifecycle: discovery, triage, development, testing, release, and deployment. Discovery identifies issues; triage assigns severity and urgency; development creates the fix; testing checks for regressions; release distributes the patch; and deployment applies it to systems. This lifecycle emphasizes rigorous testing and carefully timed releases to minimize disruption while maximizing safety.
What are best practices for testing patches before deployment to avoid issues with software updates?
Key practices include maintaining a production‑mirror test environment, validating compatibility with plugins and integrations, prioritizing patches by risk, and obtaining approvals for changes that affect critical systems. Testing helps detect regressions and ensures patches don’t break existing workflows. Documentation of tests and outcomes supports traceability and future audits.
How can automation enhance patch management to apply security patches efficiently across many endpoints?
Automation reduces manual effort and human error by centralizing patch deployment. Use patch management tools (e.g., WSUS, SCCM, or MDM) and configuration management systems (Ansible, Puppet, Chef) to enforce policies, run scheduled scans, and generate compliance reports. Tie patch deployment to vulnerability data to prioritize the most critical security patches and track progress.
What should you do if a patch causes problems—how to rollback and verify after patch deployment?
Have a rollback plan that includes clear steps to revert to the previous version, plus reliable backups or snapshots. After patch deployment, monitor services and performance, verify that fixes are effective, and confirm there are no new issues. Communicate with stakeholders if disruption occurs and keep documentation updated for future patch cycles.
| Aspect | Key Points |
|---|---|
| What are patches? | Patches are small, targeted updates that fix flaws, improve features, or adjust how software behaves. They come from vendors, open‑source projects, or independent developers and are bite‑sized changes designed to address a specific issue without rebuilding the entire application. |
| Why patches matter | They address security vulnerabilities, improve stability and compatibility, support compliance, and reduce downtime. Neglecting patches creates exposure to threats and potential regulatory or operational penalties. |
| Beyond security: performance and features | Not all patches fix problems; some optimize performance, reduce resource usage, fix memory leaks, improve error reporting, or add useful features that enhance usability and reliability. |
| Types of patches | Security patches; Bug fixes (non-security); Feature patches; Critical patches. Understanding these types helps prioritize deployment. |
| Patch development lifecycle | Discovery, triage, development, testing, release, and deployment. Each stage aims to minimize risk and maximize safety. |
| Patch management best practices | Inventory; define patch policy; test before deployment; prioritize security patches; establish approval workflows; use staging/phased rollouts; document changes; verify after deployment. |
| How to install patches | Back up data; read release notes; test in a controlled environment; schedule downtime if needed; apply the patch and monitor; validate results; document the outcome. |
| Platform considerations | Windows: WSUS or Microsoft Update; macOS: System Preferences/MDM; Linux: package managers (apt, yum, dnf, zypper); Mobile: iOS/Android updates; Third‑party apps: browsers and plugins. |
| Testing and rollback | Build a rollback plan with clear steps; keep backups/snapshots; monitor for issues; communicate contingencies to stakeholders. |
| Automating patch management | Central management tools (WSUS, SCCM); configuration management (Ansible, Puppet, Chef); scheduled scans and reporting; connect patching to vulnerability management for prioritization. |
| Common pitfalls | Patch fatigue; incompatibilities; missing dependencies; unrealistic expectations; inadequate rollback plans. |
| Security considerations | Verify patch sources; use checksums or signatures when available; download from trusted repositories; monitor vulnerability advisories and CVEs; run scanners to align remediation. |
Summary
Software patches are a foundational part of modern IT maintenance, and this descriptive conclusion examines software patches as targeted updates that fix issues, strengthen security, and improve performance. By understanding the purpose, types, lifecycle, and best practices for software patches, organizations can reduce risk, maintain compliance, and keep systems resilient amid evolving threats and technologies. A thoughtful patch management strategy—with thorough testing, rollback planning, and automation—helps minimize downtime, improve stability, and ensure environments stay current and secure.